Human Trafficking Awareness Month| RICO Act | Integrated Intelligence Strategies
- Jan 15
- 6 min read
January marks the annual awareness month dedicated to global advocacy to combat trafficking in persons. This period serves as a focal point for national and international stakeholders to convene, assess yearly progress, and evaluate performance measures aimed at dismantling human trafficking and organized crime. Throughout the month, policymakers—often in coordination with local non-governmental organizations—issue memoranda, draft legislation, and policy proposals to identify vulnerability gaps and strengthen strategies to counter the evolving landscape of trafficking in persons and organized criminal activity.

This article will briefly examine the background behind the legality of the RICO statue, its relevance to human trafficking prevention, prosecution and integrated intelligence strategies for present and future deterrence of organized crime. One model will capture intelligence led policing in Lebanon.
The Racketeer Influenced and Corrupt Organizations (RICO) Act is a U.S. federal statute that authorizes enhanced criminal penalties and civil remedies for acts committed as part of an ongoing criminal enterprise. Since its enactment, RICO has served as a powerful tool for prosecuting complex criminal conduct at the federal level. In addition to its federal application, 33 U.S. states have adopted their own RICO statutes, many of which extend coverage to state-level offenses that differ from federal crimes. The law was drafted by Robert Blakey, an advisor to the U.S. Senate Government Operations Committee, under the close supervision of the committee’s chairman, Senator John L. McClellan.

Under this law, a person who has committed at least two acts of racketeering activity drawn from the list of 35 crimes (27 federal crimes and 8 state crimes) within a 10-year period can be charged with racketeering if such acts are related in one of four specified ways to an enterprise.
Sections 1581-1592 of Chapter 96 of the United States Code (18 U.S.C. § 1581-1592), under the Racketeer Influenced and Corrupt Organizations Act (RICO), address issues of peonage, slavery, and trafficking in persons.

Organized criminal enterprises exploit financial systems to move assets and launder illicit proceeds, perpetuating human trafficking across various levels of government. Corruption among officials, whether intentional or unintentional, facilitates this crime. Examples of such corruption include assisting unlicensed or unethical recruitment agencies in the recruitment of workers for overseas employment, providing false documentation, enabling illegal border crossings, or assisting in immigration violations.
Further examples include turning a blind eye to illicit activities such as prostitution, drug cultivation, or the sale of goods produced through forced labor. Corrupt officials may also accept bribes to obstruct justice, influencing the gathering of evidence, tampering with witnesses, tipping off traffickers about pending raids, or otherwise interfering with prosecutions. Such actions extend the duration of racketeering and corruption.

One reason traffickers continue to operate with impunity is the compliance of local police and judicial officials in regions controlled by trafficking organizations. This compliance emboldens traffickers to orchestrate their activities. Human trafficking could not continue at such a large scale without the corruption within government and law enforcement. Additionally, decentralized criminal networks often complicate and distort the collection of accurate data, making it difficult to analyze relationships between actors and predict future behaviors. Human trafficking tends to be generational, with families affected by this crime often seeing subsequent generations fall victim to it. Traffickers exploit these familial ties to create systems of debt-bondage and peonage that span generations. Criminal networks rely on the active participation of all members of trafficked families, who may be groomed from a young age to assume roles within the trafficking enterprise.
Organized criminal enterprises also employ sophisticated technology to track, place, move, or sell individuals, ensuring the scalability of their operations. One case study identified a family trafficked over multiple generations, tracing back to the migration of their great-grandfather in the early 1900’s. Social network analysis revealed that the decision-making process of parents regarding their children's education and social environment was strategically aligned with the interests of traffickers. Children were enrolled in schools and neighborhoods controlled by trafficking networks involved in arms and drug trafficking.

Within families, women were recruited into sex work, financial fraud, money laundering, and others into politics and government. This example highlights how traffickers perpetuate generational crime by expanding and exploiting their networks through migration patterns and settlement trends.
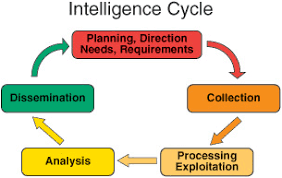
The Intelligence Cycle is the process of developing raw information into finished intelligence for use by policymakers, military commanders, and other decision-makers. This cycle consists of a dynamic, continuous, and iterative six-step process: Planning and Direction, Collection, Processing and Exploitation, Analysis and Production, Dissemination, and Evaluation. According to the Intelligence Reform and Terrorism Prevention Act of 2004 (IRTPA), the terms "National Intelligence" and "Intelligence related to national security" encompass all intelligence, regardless of its source, and include information gathered both domestically and internationally. This intelligence is crucial for addressing threats to the United States, its citizens, properties, and interests, particularly regarding the development, proliferation, or use of weapons of mass destruction and other matters pertaining to U.S. national or homeland security.

The collection, processing, and analysis steps within the Intelligence Cycle provide the framework for evaluating data and aligning it with events that may necessitate policy change. The collection phase involves gathering raw data necessary for the completion of the intelligence product. There are five primary sources of intelligence: Geospatial Intelligence (GEOINT), Human Intelligence (HUMINT), Measurement and Signature Intelligence (MASINT), Open-Source Intelligence (OSINT), and Signals Intelligence (SIGINT). Raw data can also encompass news reports, aerial and satellite imagery, and government documents. The processing phase involves specialized personnel and advanced technology to transform raw data into usable and comprehensible information. The analysis and production phase integrates, evaluates, and prepares the processed information for inclusion in intelligence products, requiring skilled personnel to impart meaning to the data. This step also ensures that the information is relevant and actionable. The planning and direction phase serves as a precursor to processing, and processing procedures must adhere to the performance standards outlined in the proof of concept.

A case study that illustrates the development of intelligence capabilities is the creation of an intelligence and analytical capacity within Lebanon. Rather than reacting to events, this intelligence-led approach is tasked with identifying trends and patterns based on existing knowledge, which is then used to guide decision-making. In this case study, the Lebanese Internal Security Forces (ISF) partnered with London’s GIAC and sought to deploy resources more efficiently to address evolving safety and security needs.
Major Lebanon threat actors include Hizballah, ISIS, Hamas and Abdullah Azzam Brigades. The ISF faced challenges related to bottlenecks and inefficient paper-based workflows. They also identified that operational data was not optimally utilized in decision-making regarding mission planning and resource management. The integrated intelligence strategy aimed to support the ISF in creating an intelligence-led policing framework with redesigned workflows, automated processing of manual tasks, and digital tools to aid data collection, analysis, visualization, and decision-making. This strategy led to the establishment of six Command and Control Centers across Lebanon, digitally linked to 22 regional operations rooms.

Additionally, specialized personnel were trained in analytical techniques, and a planning team was formed. The training included accredited lessons on how to collate, audit, and process data to produce analytical products that inform decision-making. The ISF also institutionalized a performance management framework across all command centers, allowing for systematic analysis of policing priorities, crime reduction indicators, and performance monitoring. The intelligence integration program culminated in the development of a bespoke digital platform, FENIX, which facilitates the capture and analysis of crime and operations data. This central interface enables data collection, auditing, crime trend analysis, and performance auditing, used uniformly across all departments.
The proof-of-concept phase marked the transition to analysis, production, and dissemination within the intelligence cycle. The initial analysis and planning unit was established in Beirut in 2017, and the development of the ISF’s incident, crime, intelligence, and case management system, FENIX, was implemented. The operation rooms supported data capture and reporting, enhancing the data facilitation process. Accredited courses on Intelligence Analytical Techniques were developed for the ISF, leading to the formation of Strategic and Tactical Tasking and Coordination Groups. Strategic and Tactical
Assessments were subsequently used to inform decision-making and operational activity within the ISF.

The outcomes of this intelligence integration program have been substantial. There are now seven analysis and planning teams stationed across Lebanon, with over 120 analysts and planners trained and mentored. Four key intelligence reports have been produced, focusing on strategic, tactical, problem, and subject-specific areas. Notably, 40% of the analysis and planning team staff are female, promoting gender inclusion in operational roles. Over 120,000 incidents have been logged on the digital policing platform since 2016, and more than 96% of command-and-control center users report that the digital platform has contributed to operational improvements.
Modern espionage networks increasingly operate as decentralized criminal enterprises. They exploit commerce, academia, social media, shell corporations, and technology platforms to acquire sensitive information. OSINT has become the primary terrain through which foreign intelligence services initiate recruitment, influence operations, cyber intrusion, and intellectual-property theft.

Current RICO provisions do not mandate OSINT-based threat assessment tools for identifying foreign enterprises acting against U.S. national interests. Without OSINT integration, DOJ and partner agencies lack systematic visibility into digital patterns of racketeering, especially those originating abroad. Such digital patterns include publicly accessible, rigorously verified database of Chinese influence and espionage incidents in U.S. academic institutions, think tanks, and research partnerships.
Under current federal interpretation, civil RICO plaintiffs may only recover for injuries to business or property. Victims of human trafficking, environmental harm, unsafe housing, contaminated products, or targeted violence cannot pursue RICO damages for personal injury even when those harms result directly from an enterprise’s racketeering activity.
This limitation disproportionately affects low-income families, trafficking survivors, and individuals harmed by criminalized commercial practices. Recognizing personal injury under RICO would allow victims to seek meaningful relief in instances where bodily harm is the predictable and intended outcome of an unlawful enterprise.
January is Human Trafficking Awareness Month.

























Comments